Key Takeaways
DDoS attacks aim to disrupt network traffic by overwhelming servers. Understanding the nature of DDoS attacks is crucial for implementing effective prevention strategies.
Implement rate-limiting and web application firewalls to mitigate DDoS attacks. Proactive measures like rate-limiting and WAFs can help distinguish legitimate traffic from malicious attacks.
Anycast network diffusion can disperse traffic across multiple servers to prevent DDoS attacks. Utilizing Anycast networks can help diffuse traffic before it reaches critical servers.
Consider investing in DDoS protection services for enhanced security. Leveraging high-powered security solutions can offload the burden of managing complex security measures.
Normally, any website owner would welcome internet traffic. However, there can be times when network traffic can be disruptive. When this kind of cyber attack occurs, it is most likely a DDos attack. Why do they occur? Any DDos attacker who instigates this malicious traffic either wants the attacked network to stop functioning or hold it ransom until the owner pays them to stop.
With distributed denial-of-service (DDoS) attacks becoming more advanced, more forceful, and more prevalent in today’s digital world, DDoS mitigation has become an integral part of your technology stack.
But stopping DDoS attacks is far from a simple process, and finding the right way to mitigate this type of malicious activity is different for every organization. That said, there are several proactive steps you can take to prevent DDoS attacks from succeeding.
Before we dive in, it’s important to understand what exactly a DDoS attack is.
What is a Distributed Denial-of-Service (DDoS) Attack?
How do you distinguish a DDos attack from legitimate traffic? At its core, a distributed denial-of-service (DDoS) attack is a harmful attempt to disrupt normal traffic of a network or server by overwhelming the infrastructure with a massive flood of traffic. Think of it like being stuck in a traffic jam. You’re trying to get somewhere, but you can’t because of all the other traffic on the highway. In this scenario, a DDoS attack is the traffic jam preventing you from getting to your final destination, and the attackers are not only obstructing the roads but also contributing to the volumetric attack. There are a lot of different types of DDoS attacks, but for this post, I’ll list a few of the most common types:
- HTTP Flood
- Protocol Attacks
- Volumetric Attacks
- DNS or UDP Amplification
- Layer 7 Attack (Application layer)
How to Prevent a DDoS Attack
Now that you understand what a DDoS attack is, what are some steps you can take to prevent one from happening? A lot goes into preventing a DDoS attack, but it can be broken down into a few simple stages.
The biggest factor is separating legitimate traffic from malicious traffic. As mentioned above, there are a few different kinds of DDoS attacks and sometimes we even see multi-vector DDoS attacks, in which there are separate layers of the attack all happening at once.
Nonetheless, a common way to mitigate a DDoS attack is to implement rate-limiting. This means the number of requests a server can accept within a certain timeframe has been limited. While this is a useful element of DDoS mitigation, it won’t work when dealing with larger, more complex attacks.
When it comes to preventing larger-scale DDoS attacks, using a web application firewall (WAF) and Anycast network diffusion comes into play. Anycast is a network addressing and routing methodology in which a single destination address has multiple routing paths to two or more endpoint destinations. Essentially, the Anycast network disperses traffic across a wide array of servers, which in turn diffuses the traffic before it gets to your server.
A WAF can also help mitigate the very common Layer 7 Attack by placing a set of rules between the origin server and the Internet, which acts as a gatekeeper and protects the server from malicious traffic.
Now, implementing and configuring any of the above manually, on your own, can be a daunting task, especially when you consider that the solutions we’ve covered are far from the more advanced security precautions available. But daunting doesn’t mean impossible. Setting up a WAF on your server involves, but is not limited to, installing and configuring OWASP. This is a relatively straightforward process that involves installing mod_security on your Linux server and using a repo on GitHub to do a few simple clones.
Setting up an Anycast network is a little more tedious and has a higher cost associated with it. In order to set up an Anycast network, you would first need to have servers or nodes set up in multiple data centers regionally, and globally. Once you have those servers set up, you need to configure your network to route the incoming requests so they’re dispersed across your servers using a specific prioritization method.

DDoS Protection
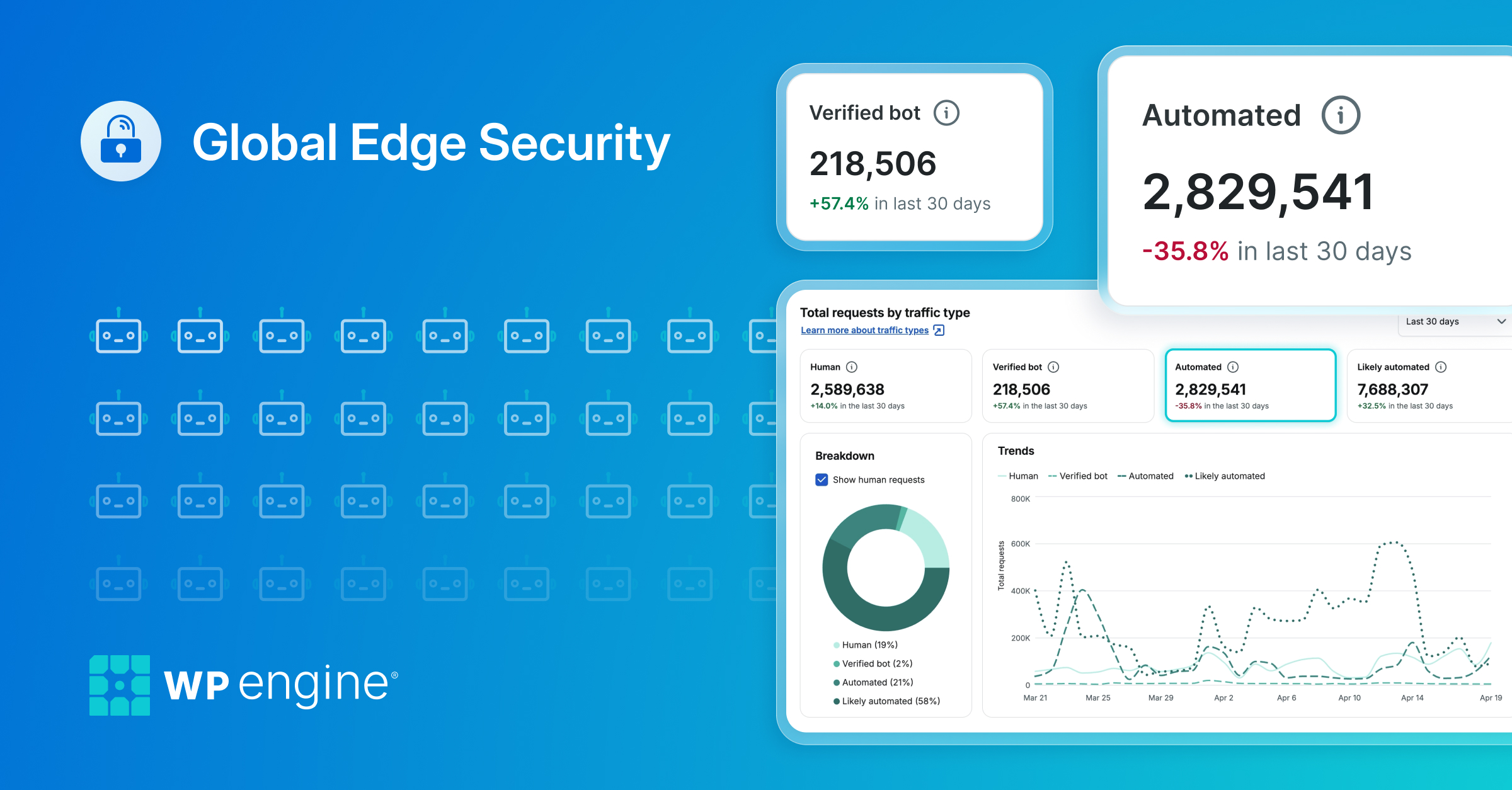
So, how do you stop a DDoS attack? You can implement a WAF, set up and use an Anycast network, and maintain a cluster of servers on your own. Or, you can use an existing, high-powered security solution like Global Edge Security, in addition to the DDoS mitigation tools that come with WP Engine’s standard managed hosting plans for WordPress. Your website security could benefit from our DDoS protection service.
In choosing an enterprise-grade cyber defense built specifically to secure your WordPress site(s), you’re free to focus on your business, as opposed to maintaining Anycast networks, WAF rule sets, or which security patches you need to apply to your servers. To experience these benefits, consider investing in DDoS attack protection.
Find out more about WP Engine here or reach out to a representative with your questions!